Recently, we had a chance to help a user who received a suspicious message. Unlike thousands of other Internet users, instead of clicking links indiscriminately, he followed his hunch and called us. It turned out that he had experienced an unknown type of attack.
The attack described below is only a couple of days old and we had not encountered it or its description anywhere before. It looks like the target group has been rather limited so far. In our case, it was a law firm, but we advise everybody to be wary of false Microsoft Office plug-ins because they are fairy convincing.
An ingeniously prepared attack.
Our hero of the day runs a law firm (a real one, not the kind which sends demands for payment to the Internet users). On Wednesday, a message was found in the firm’s mailbox with the subject: “Inquiry about cooperation and scope of business?” The content of the message was as follows:
Hello, I am writing to request information about legal service for the Polish branch of our company, which is currently being established. I was assigned a task to gather information and get in touch with potential service providers of our company. I found your contact details on the Internet and at this point I am interested in preliminary information about the scope of your services. Do you have a “Price list” which you could present to us?
If you need any information from us, I will be pleased to supply you with a document with a description, in Polish, of the requirements/recommendations set by the company. Meanwhile, I would very much appreciate a specification of your services. The matter concerns a business enterprise operating in Poland.
I am looking forward to your reply and to mutually beneficial business relations.
Yours faithfully, Marek Błaszczyk Technical Coordinator - Poland EuroLogistic Courtensdreef 339, 4040 Herstal [email protected] +0471 55 84 19 +0471 55 84 22
The message did not arouse any suspicion. The lawyer responded, explaining the range of services his firm offered and asking several questions. On Friday, he received another message with the title: EuroLogistic, details of business relations for the Law Firm? and the following contents:
Hello again, First, let me apologise for the delay in answering, but we are currently organising our business enterprise. I am sending this message to you from my personal mailbox as I would like to keep the correspondence in one place.
Thank you for getting back to us and let me shed some light on the type/scope of services we would be interested in.
The Polish operation is a subsidiary of a Belgian company. We are registered with a VAT number in Poland and in the EU.
We are seeking legal advisory services for a business entity in Poland for the following purposes: – staff organization (civil-law contracts) – negotiating, reviewing and drafting business contracts (particularly with new partners) – potential collection of debts, protection from unreliable clients – legal representation ad litem, if required – potential assistance in the expansion of the company’s organization (real property)
The company is a forwarding/logistics enterprise, however, management is seeking to diversify the business so under one corporate name there is also a wholesale branch (mainly dealing in foodstuffs). At present, we have nearly 300 regular employees and 100 seasonal ones in the EU (except Poland). We generally aim to hire about 40-50 employees with different job descriptions in the area (country) of operations.
I am aware of the fact that the above information is still rather general, but I have sent a request to the central service office for a task specification (current and forthcoming) which we would like to engage you to do and a draft of agreement, which will naturally be up for negotiation. I have included the information received from you and in response, also our expectations regarding the cost of service have been added in the document, whether or not it will be on an occasional basis or on the basis of a fixed contract.
The file is digitally signed and is for your eyes only. http://docs.logisticservers.eu/?fname=polska_filia_eurologistic_uslugi_wymagania.docPlease, read the document, and however much time you need to get back to us with your offer, I am at your service. However, my response may be delayed by several days as I am going on vacation leave.
Yours sincerely, Marek Błaszczyk
Seeing a link to the file, the lawyer chose to find out more about it instead of just clicking the link and this is how he reached us. We were unable to deal with the matter on Friday and so it waited until Monday. What we found took us completely aback.
Points for creativity: 10/10
The link included in the message directs the user to a partially familiar-looking page. Anyone recognize the header?
First stage
It looks a bit like an embedded PDF reader, doesn’t it? Then another screen appears...
Second stage
Many of you are also bound to know the second screen - a loading Microsoft Office document. The percentage is changing, so are the steps. Until we reach the first culmination:
Third stage
You have probably guessed that the click on the “Fix” button transfers us to the download page of an executable file. Here is its address:
http://update.microsoftcenter.eu/download/WcPlugin.exe
The WcPlugin.exe file is definitely malicious - but we’ll tell you more about it later.
What we know about the attacker’s infrastructure
Our attempt at verifying the company which sent the inquiry leads us to the eurologistic.be site, which welcomes us as following:
Eurologistic.eu website
The contact details displayed on the site are consistent with the ones provided in the email, though the links to Twitter or Goldenline do not work. The e-mail messages which this story starts from were sent from [email protected] and [email protected] addresses by means of two mass mailing sites - MailChimp (the former) and MailJet (the latter one). Both the sites have SPF entries in the DNS record of the domain. The eurologistic.be server even offers an interface for a distribution list based on phpList, thanks to which one can unsubscribe from further messages.
The eurologistic.be domain was registered on 16 August 2015 at 14:47 by a user who stated the address of [email protected] and it is ascribed to machine 94.249.147.76 in a UK server room. The first email message was sent from the same server.
The logisticservers.eu domain (hosting the page with the “document”) was established on 19 August 2015 (last modified at 9:57) by a user who stated the address of [email protected] and it is ascribed to machine 185.61.148.226 in a Latvian server room. It can be traced to the sachermasoch.ru domain, which has a bit longer history:
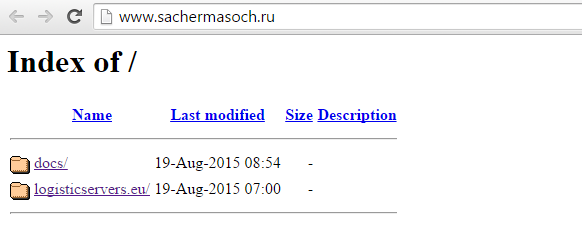
sachermasoch.ru
The microsoftcenter.eu domain (hosting the EXE file) was registered on 19 August 2015 (last modified at 10:39) by a user who stated the address of [email protected] and it is ascribed to machine 67.227.164.121 in a US server room.
The cannedgood.eu domain (the server which the malicious EXE file connected with) was registered on 11 August 2015 (last modified at 15:08) by a user who stated the address of [email protected] and it is ascribed to machine 185.53.130.200 in a Dutch server room.
It looks like that the culprit skilfully altered the crime scene
When we tried to find traces of any earlier malicious use of this infrastructure, similar messages, infection methods or similar EXE files, we either got nothing or only faint traces.
It seems that a file from the same WcPlugin.exe address had been first reported to VirusTotal on 22 August, yet no file analysis was available. It was reported there for the second time on 23 August:
MD5: 5c8ce6e2731ba69e8b46cb2e33ae2cad
SHA1: d399ebc731dde44a9ef48be295ebfe8f164c7868
The file we found on Monday had not been reported to VirusTotal before and was recognised by only 5/56 antivirus programs.
MD5: b1b4f264d83c22a822ee9137a8b4406b
SHA1: acb4d5758d9c68c149a4c4ca072a7c838dcf48db
On Tuesday we managed to get another version, recognisable to 6 out of 56 antivirus programs.
MD5: a5fe7dc1179ab42866bc18f2cd2d6921
SHA1: 6025bc310fa092c9814d9d5345c7cd96c1aecf75
We also managed to find information that in July the 94.249.147.76 server had hosted a phishing site http://secure.mojepayu.com, though there is no other connection with the attack described above. Google found no traces of the emails pasted above nor the messages displayed during the infection process. If you have seen this attack before - let us know.
Provisional summary
You have to give it to the attacker that he did a lot of work. For the purpose of the campaign, he registered several unrelated domains, which he located in different server rooms all over the world. He composed email messages, taking care of their relevance and credibility to the recipients (our lawyer did not found anything out of the ordinary). The attacker used a rather professional language in the correspondence. He set up the servers in such a way as to maximise the likelihood of the message reaching the recipient. He is conducting the campaign quietly - so far it has left no traces anywhere in the web.
The EXE file itself is also rather unusual - it is a standard InstallShield installer which plants a Microsoft Office plug-in on the victim’s PC along with, naturally, extra elements. Those unsolicited files are doing their utmost to prevent their analysis so you will have to wait a little bit longer for the second part of the description. In the meantime, make sure to notify us if you come across a similar attempted attack.
What to do if you have clicked the link, downloaded and opened the file mentioned above?
We do not know yet what the malware was supposed to do, so we suggest taking the following steps:
- unplug the computer from the network,
- back up important files,
- format the disk,
- reinstall the system,
- change all the passwords for everything,
- check your bank account history,
- notify the clients whose contact data were in the mailbox and on the disk,
- estimate the worst case scenario assuming that somebody got hold of the copies of your law firm’s files and mailbox and obtained access to all the sites which the law firm had access to.
Updated 2015-08-25 11:22
We now know of at least 4 other cases of attacks on law firms. The oldest occurred on August 17, around 5:00 p.m. All the messages look the same.
The file with the Trojan horse has disappeared from http://update.microsoftcenter.eu/download/WcPlugin.exe and the following record appeared on the home page:
POkemon catch them all Thank you for your time, but, guys, look how this poison will spread now
There was supposed to be a picture of the Fiat 126p below, however the author missed a key and the photo won’t show. Where the document was served from now this text appears:
Big deal, that was not so cunning, come off it now. Thanks Adam for weeks of my work going down the drain. Restart.
Click Alt+F4 to see hidden contents! Fiat126pTeam
A model WcPlugin.exe file with its analysis can be downloaded from hybrid-analysis.com. As usual, we would like to invite the author of this attack to give us an interview - contact us any way you like.
Updated 2015-08-27
An analysis of the malware used in the attack is now available - go to CERT Polska site for a description.
If you are interested in raising the awareness of your staff in order to be better protected against such attacks, have a look at the SecurityInside service.





Comments