Afraid of missing important security news during the week? We’re here to help! Every week we put together a curated list of all important security news in one place, for your reading pleasure. Enjoy!
For the less technical
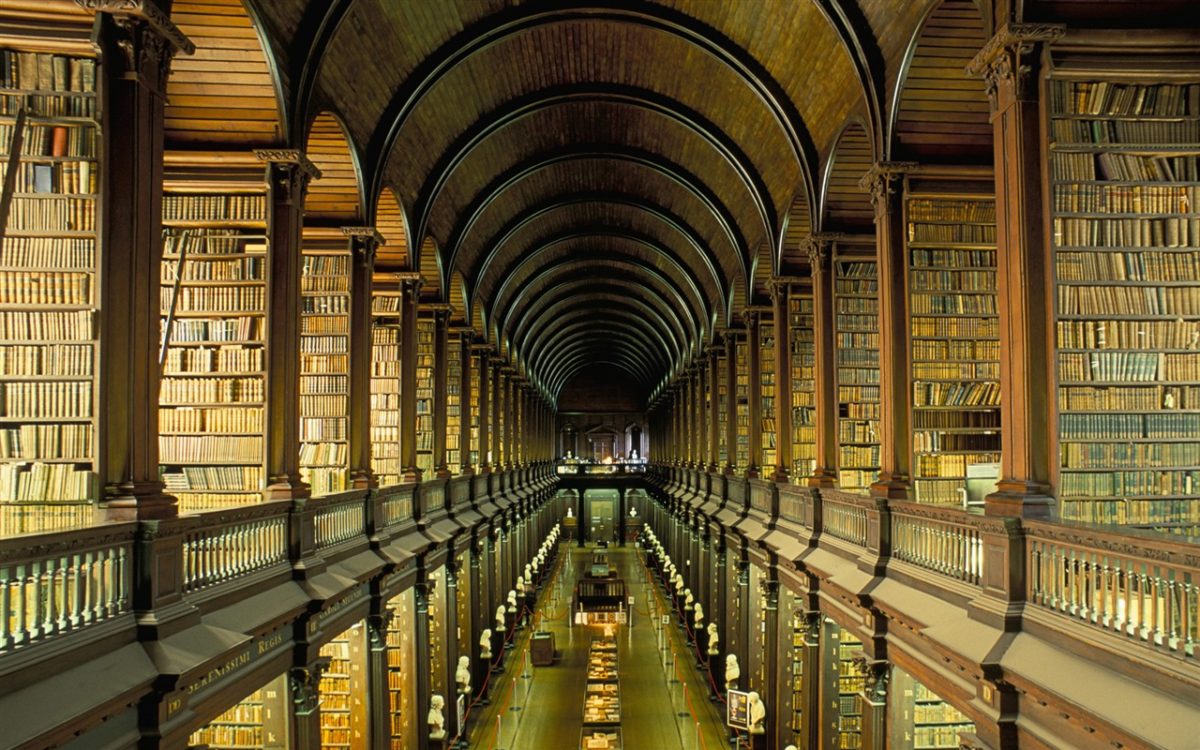
- Story of a professional book thief
- How a fictional agency received military equipment worth a million dollars
- Working at a numbers station
- How Moscow protects itself from cyberattacks
- How US tried to defend the elections
- Creating a spy’s cover
- UAE behind Qatar attacks
- Losing money because of password reuse
For the more technical
- [VIDEO] John Salomon from FS-ISAC about cooperation in financial sector
- RECON 2017 slides
- Cyber Threat Intelligence reading list
- Patching SambaCry by exploiting it
- RFID fuzzer
- WannaCry and NotPetya comparison
- Hash Buster to do online hash lookups
- Windows Defender new features
- Ethereum multi-sig wallet hack
- Millions of cameras vulnerable
- Paypal server RCE
- Outlook rules as backdoor
- NTLM hash leaks
- Rurktar – spyware under development
- Mass LinkedIn data download
- Malware campaign analysis
- EternalBlue vulnerability stats
- Thermostat vulnerability and attack example
- Symantec revoked the certificate based on fake private key plus Symantec’s response
- EnglishmansDentist analysis
- [PDF] Midyear Cisco Cybersecurity Report
- [PDF] Darktrace network anomaly report
- Stantinko – huge malware campaign
- RCE in Valve games
- Estimating vulnerability rediscovery
- Extracting WhatsApp messages from iCloud backups
- Darkweb gun trade
- Boss detection system
- First Czech radiotelephone network
- Many critical update from Apple
- New edition of CIA leaks
- Audit results for Firefox Accounts
- Real world attack with Rubber Ducky
- WSJ paywall bypass
- Backdoor hidden in a JPG file
- VMWare attack analysis
- CoinDash ICO attack
- MySpace account takeover
- Apache fuzzing
- How was Zcash created
- Gandi.net domains takeover
- Twitter botnet analysis
- Android backdoor / RAT
- Vulnerable Memcached servers availability analysis
- Google improves warnings
- Dark Hotel campaign analysis
- Hoverboards vulnerabilities
- Tor Project’s bug bounty
- Android AV limitations
- PS4 SDK leak
- Ransomware anatomy
Did you enjoy this list? You can subscribe to one of our feeds on Twitter, Facebook or RSS.

One thought on “IT Security Weekend Catch Up – July 24, 2017”