Today we want to show you how creative can Polish bank robbers get. We’ll cover the full internet banking theft scenario, starting with a simple FB account takeover and ending with full bank account balance stolen and converted to BTC on thief’s wallet.
It all starts with a Facebook account takeover. The source for account credentials can be either malware or phishing and while most users still don’t use 2FA and thieves know how to use socks to spoof user location, the takeover can be easily performed. Once logged into a victim’s account, the thief starts going though chat history to pick further victims in good relationship with the FB account owner. After a thorough analysis of a particular conversation, given between a grandson (initial victim) and grandma (secondary victim) a new conversation in the same style and voice is started by the thief:
Hi Grandma, can you top up my prepaid phone with 22 PLN?
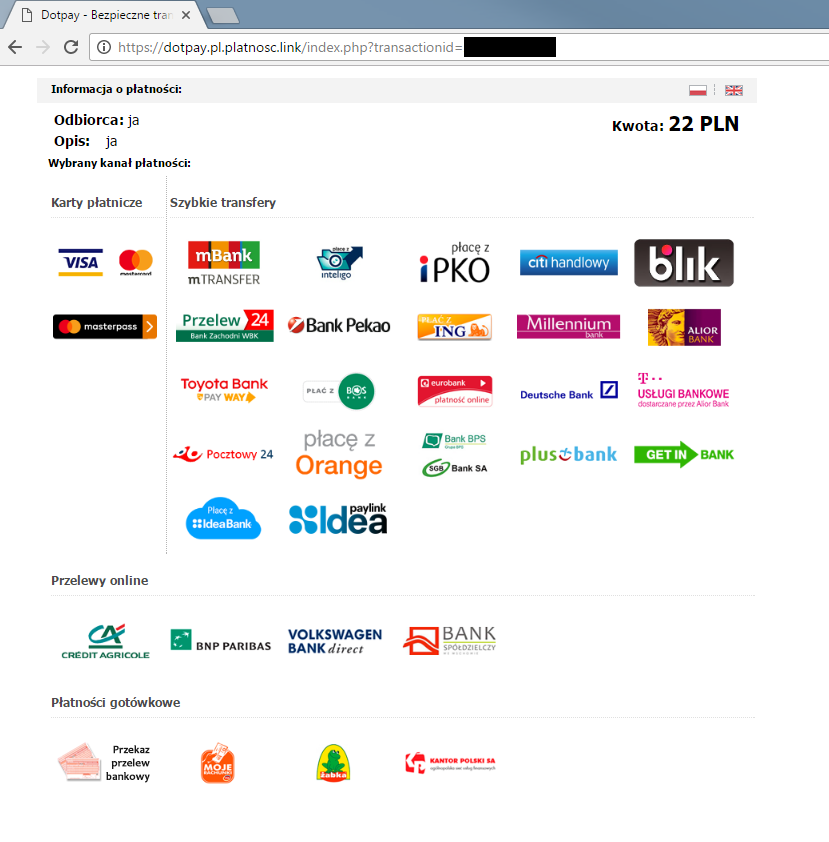
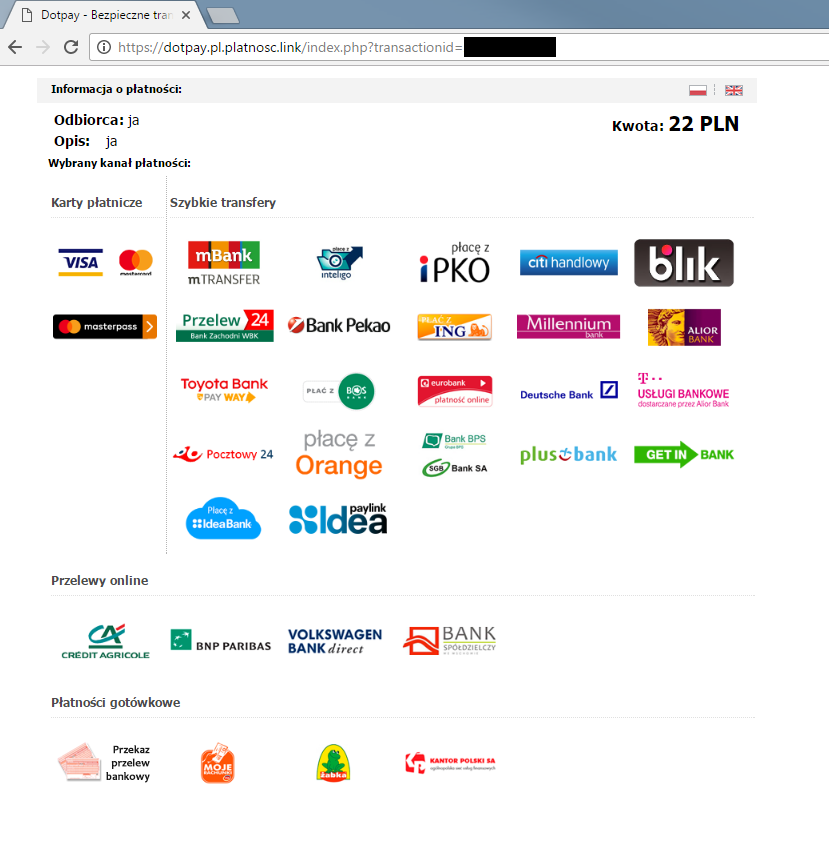
If grandma agrees to pay 22 PLN (around 5 EUR), she receives a “payment link”, in this case
https://dotpay.pl.platnosc.link/
DotPay is a Polish payment provider, “platnosc” is “payment” in Polish. Payment intermediaries are very popular on the Polish market – they have contracts with all major banks and make internet shopping without a credit card an easy process. During the checkout the user clicks a payment provider link, logs into his bank account (on the bank website) and has all the information needed for the transfer already filled in. He has only to provide the one time code received by SMS to finalise the transaction and the transfer happens immediately.
Our thieves decides to mimic the website of one of the payment providers. While the fake website was still functional (it moved yesterday), it looked like that:
Once Grandma decides to help her grandson and chooses her bank on the fake payment provider website, she is redirected to a fake bank login panel in the same domain. Examples for some of the most popular banks in Poland below:
One clever trick
The thieves discovered a simple, yet clever trick to make sure that the SMS message will read “transfer of 22 PLN” while in reality the code will also approve creating a so called “trusted transfer”, which will enable them to perform further transfers to the same account number without additional authorization via SMS codes. Some variants of this scheme have been observed in Poland a few months back, but the thieves are still improving it. This is their latest scheme as seen in the last two weeks in Poland.
For the sake of usability most banks offer their customers the ability to add a given account to the “trusted” ones while also performing the bank transfer. It’s just one additional tick in the transfer form. Unfortunately approving one transfer can also mean that all further transfers to the same account will also be approved.

The text in the red frame means “Add to the recipient list”, which means “won’t ask for SMS code for future transfer to this account number”.
The last hurdle for the thief is a wise choice of the bank account number that will be set up as trusted – it usually is a mule bank account which has been prepared for the fraud. The same mule has already created an account at one of Polish bitcoin exchanges and sent some funds there to establish a regular transfer pattern (to avoid the bank calling and asking “are you sure you want to speculate with cryptocurrency today”). The “transfer” account is usually chosen to be in the same bank as Grandma’s account (for quick transfers) and once the money is stolen from Grandma’s account it takes less than 15 minutes to turn it into bitcoin. Another variant is a direct transfer from Grandma’s account to the bitcoin exchange.
Summary
The whole scheme is hard to prevent by the banks as it mostly happens outside their scope of action. It begins on Facebook, then moves to fraudster’s hosting and the thief logs into the bank using mostly socks ports on zombie machines in the same area where the victim lives. Only vigilant fraud detection departments equipped with proper detection mechanisms can handle those attacks properly. Fortunately for the victims those scenarios don’t scale well, but a handful of attempts can be noted in one evening.




That’s not true. “Dodaj do książki odbiorców” does NOT remove SMS authorization in mBank. There’s a separate checkbox in the recipient list for that.
Two things:
Firstly, not every bank requires a SMS confirmation, I am not asked about it in ING often;
Secondly, a small mistake: “Our thieves decides”.}
Cheers